
Cybersecurity
Bachelor of Science
Overview
Cybersecurity involves the responsible stewardship of information and trust. Our graduates will have the character training, communication skills, plus technical expertise to allow them to excel in this field.
Our cybersecurity program gives you foundational knowledge in programming, databases, networking and operating systems so that you know what you are to protect and how it is vulnerable. The phrase “wise as serpents and harmless as doves” describes how you will be prepared. You will know how systems could be compromised but will also have the character to be entrusted to protect against such attacks.

Program
During your first year, you’ll learn two programming languages: Python and Java. Demand for skilled programmers in these languages is strong. Additionally, you’ll be introduced to various software development skills such as web app development, GUI programming and team programming. Penetration testing and ethical hacking is a part of your second year and is used to explain and motivate the study of various fields of computing such as networking, operating systems and databases.
Computer security, cyber operations, applied cryptography, and reverse engineering of hardware and software are some of the upper level courses in the program. Your senior year also includes opportunities for a cybersecurity internship and participating in the cybersecurity seminar course.
Your courses will equip you for entry into security fields, general software development, and also graduate programs for research in cybersecurity.
BJU Core
Having a broad base of knowledge and experience will help prepare you for whatever opportunities the Lord brings your way. Bible and the liberal arts courses (such as history, economics, English and speech) will give you the tools to relate to a wide range of people and to clearly communicate. We want to equip you to be a fruitful, flexible servant of Christ.
Electives
The cybersecurity program prepares you for a variety of careers. Your electives may be taken to strategically position you. Interested in cybercrime—take electives in criminal justice, interested in defending your network from phishing attacks—take a course or two in psychology, or take communication or management skills to open more doors. These courses may be just what God will use to specifically prepare you for work and service
Your Future
Jobs
The cybersecurity program at BJU opens the door to many career possibilities including:
- Security analyst
- Secure software development
- Security administration
- Security officer
- Penetration tester
- Security architect
- Digital forensics
- Network manager
- Cybercrimes unit member
Career Options
While there are many jobs in the cybersecurity field, you might choose to go into more traditional computer science or information technology jobs such as software developer, database administrator or network engineer. You could also use your skills to assist churches, missionaries, Christian ministries and Christian schools.
Career Support Assistance
BJU offers students a variety of ways to network with employers and organizations. A multitude of job opportunities are posted each year on Career Central, our online job board. In addition, over 60 businesses and 150 Christian schools/mission boards/Christian organizations come on campus to recruit students through on-campus interviews and job/ministry fairs. The Career Services office also helps students by holding seminars on resume preparation and interview techniques.
Learning Experience
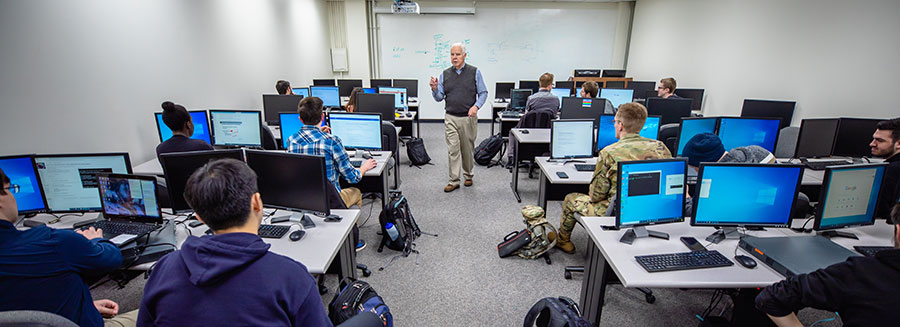
Computer Labs
You’ll have access to multiple well-equipped computer labs around campus. BJU provides both standard industry hardware and software and cutting-edge technology so you will have a firm grasp of the basics and the ability to adapt to an ever-changing field.
Lab Assistantships
Our upper-level cybersecurity students gain on-the-job experience as lab assistants. You will benefit from their debugging and testing skills as you become familiar with the major. Eventually, you will have the opportunity to apply for the position and share your experience of finding memory leaks and buffer overflows with others.
Capture-the-Flag Contests
Contests such as capture-the-flag (CTF) and collegiate cyber defense competitions allow you to practice the skills that you have learned. These contests are a new venue of competition for our students. We have competed intercollegiately for almost 20 years in programming contests, but we are just getting started in the cybersecurity field.
Internships
Employers in the Greenville area recognize the high caliber of our students and often seek them out. Our students have interned at local and out-of-state companies including Booz Allen, Oak Ridge National Laboratory, Answers in Genesis, Worthwhile, and Follet Software Corp/Tetradata.
Intercollegiate Programming Contests
BJU students have the opportunity to compete alongside other Southeastern universities including Georgia Tech, Mercer, Wofford and Emory. In recent contests, several of the BJU teams have placed in the top five out of 20-30 teams.
Faculty

Department of Computer Science
Our primary cybersecurity faculty members average 30 years experience in information technology and computer-security research and development. They have worked with large companies such as Blue Cross and Blue Shield of Georgia and also defense companies like Raytheon and Lockheed-Martin.
The broader computer science faculty have practical experience in addition to classroom training. They’ve spent time in the industry in consulting, directing web development, and optimizing freight transports. These experiences provide a rich pool of examples that are shared with the students.
Courses & Objectives
Sample Course Outline
1st Year
2nd Year
3rd Year
4th Year
- Applied Cryptography
- Foundations of Economics
- Worldview & Apologetics
- Applied Cybersecurity or Internship
(3 credits) - Electives
(3 credits)
- Program
- BJU Core
- Elective
Program Objectives
Each student will:
- Apply introductory cybersecurity principles to both policy and practice.
- Design, implement, and evaluate a computing-based solution to meet a given set of secure computing requirements.
- Apply security principles and practices to maintain operations in the presence of risks and threats.
- Communicate technical information effectively, including risks discovered and mitigation strategies.
- Apply biblical principles of ethics in computing.